Restoring an Active Directory Backup

Full-Access Members Only
Sorry, this lesson is only available to Server Academy Full-Access members. Become a Full-Access member now and get instant access to this and many more premium courses. Click the button below and get instant access now.
Instructions
Q&A (0)
Notes (0)
Resources (0)

Saving Progress...
Resources
There are no resources for this lesson.
Notes can be saved and accessed anywhere in the course. They also double as bookmarks so you can quickly review important lesson material.
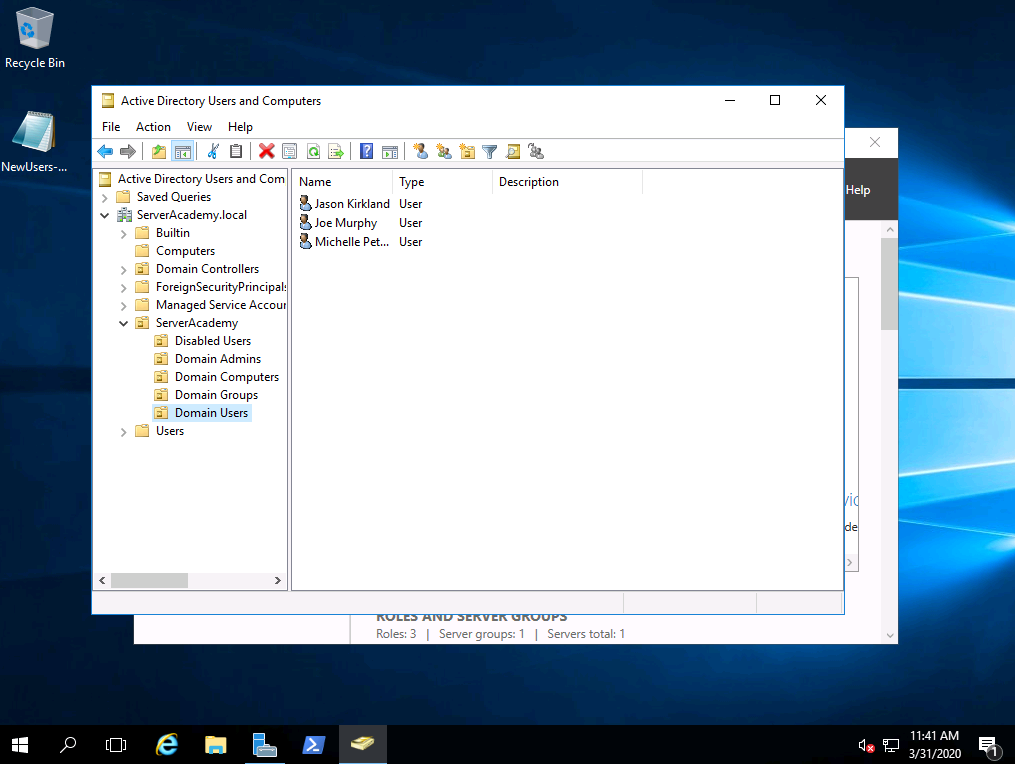
In this lession, we will be restoring an Active Directory / System State backup of our primary domain controller. To get started, I am going to log in to my test lab, open Active Directory and start breaking stuff.
I’m going to delete the root OU I have called “Server Academy”. This will delete several user and computer accounts as well as other sub OUs.
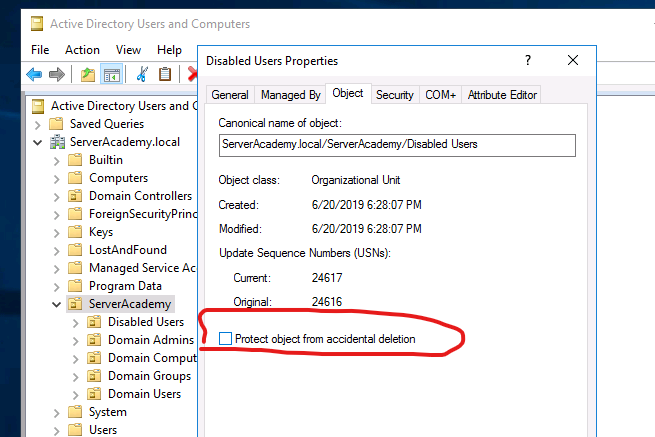
First I need to enable Advanced Features by clicking View > Advanced Features, then I can open the properties of each OU and remove the protection from accidental deletion:
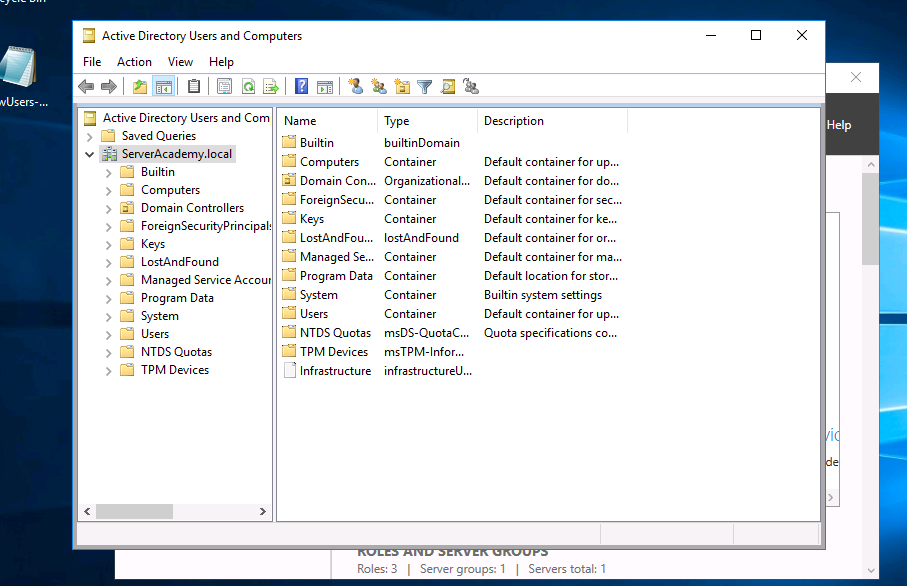
Now that I have repeated this for all the OUs, I can go ahead and delete the OUs:

So now my OU and User Accounts are deleted:
Yikes! Now I need to restore my backup to get the data back. To restore a System State backup of an Active Directory we first need to boot the server into DSRM (Directory Services Restore Mode). We can boot into this mode by restarting the server and repeatidly pressing F8 from the moment the server powers off until you see the screen below:

Select Directory Services Repair Mode, then press Enter.
Notice: If you don’t have physical access to the server or don’t see the prompt when you reboot the server, use MSConfig:
Then select Boot > Safe boot > Active Directory repair:
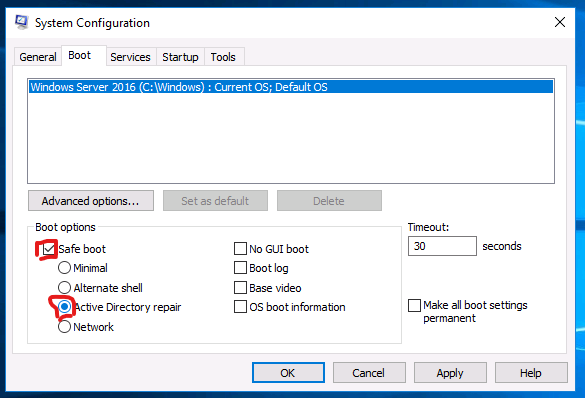
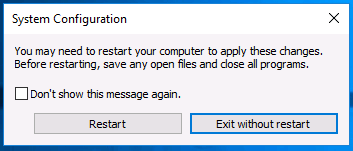
Click OK then restart:
Once you have rebooting into DSRM mode, log in with the LOCAL administrator account and the DSRM password you created when you installed the ADDS server role:
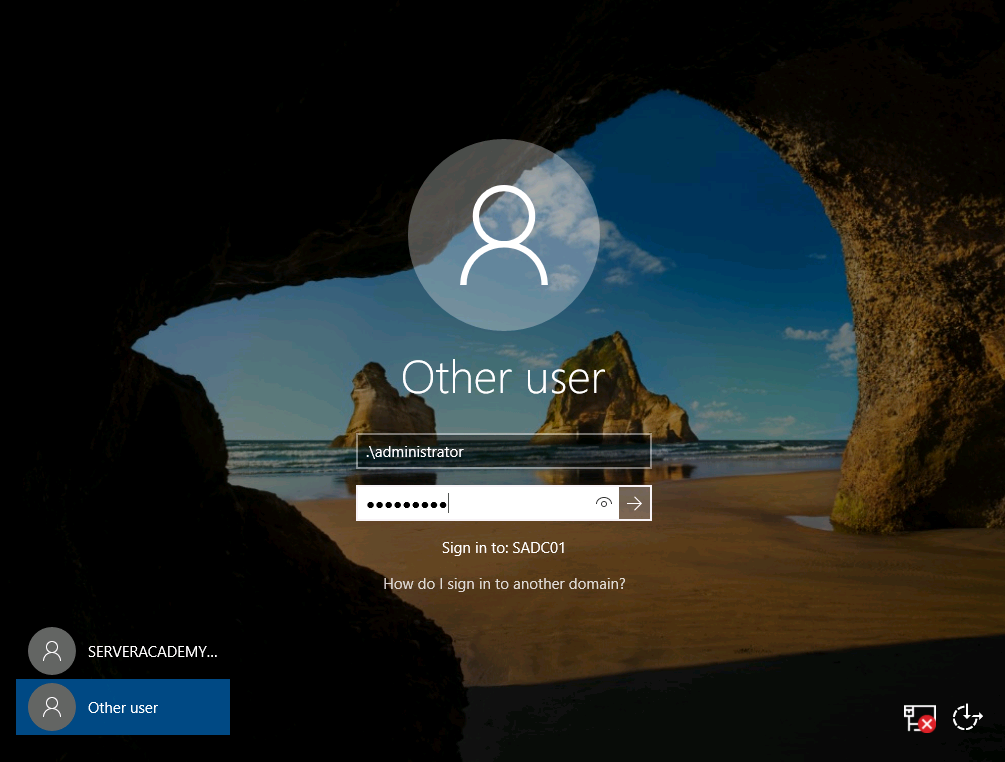
If you see a message about no logon servers available, that means you are using a domain account and not a local account.
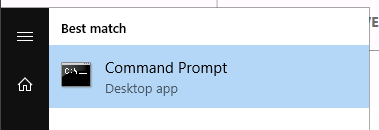
Once you’ve logged in, open Command prompt:
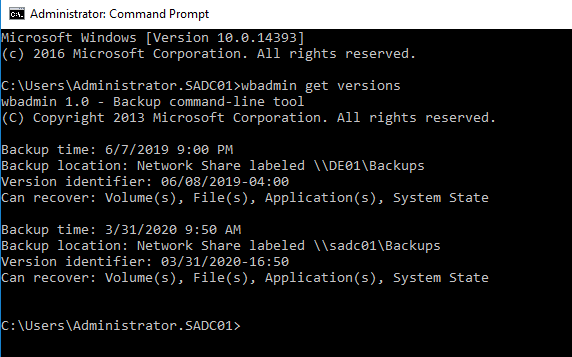
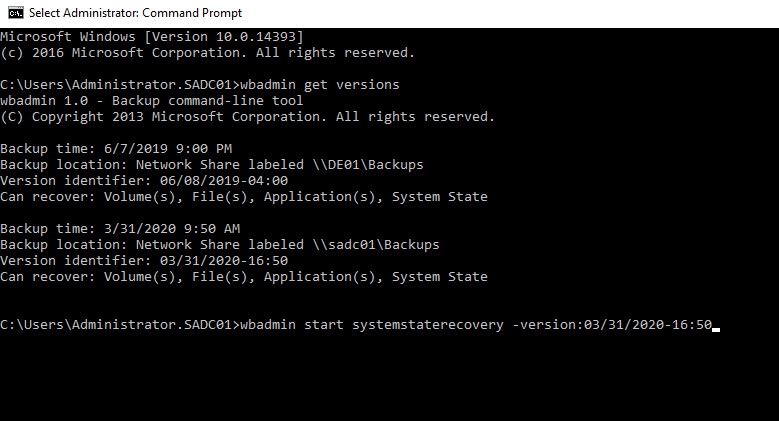
Next run the following command:
wbadmin get versions
Next start a recovery by running the command:
wbadmin start systemstaterecovery -version:[Insert your version identifier here] –authsysvol
Note that the “–authsysvol” marks this sysvol as the authoritative for your replication.
I am going to select the latest update I have, and run the command:
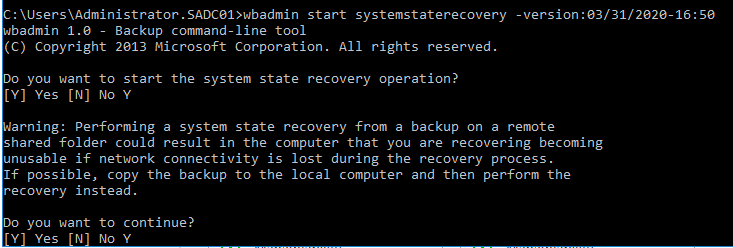
Next enter “Y” to confirm:

Again type “Y” to confirm that you may lose internet connectivity:
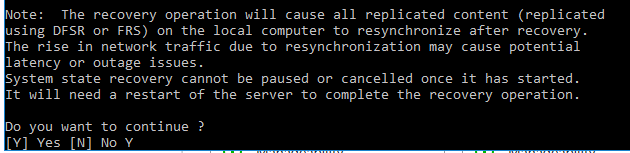
Confirm that you understand there will be increase network traffic between your domain controllers (if you have multiple) due to AD replication:
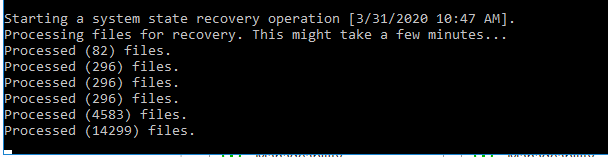
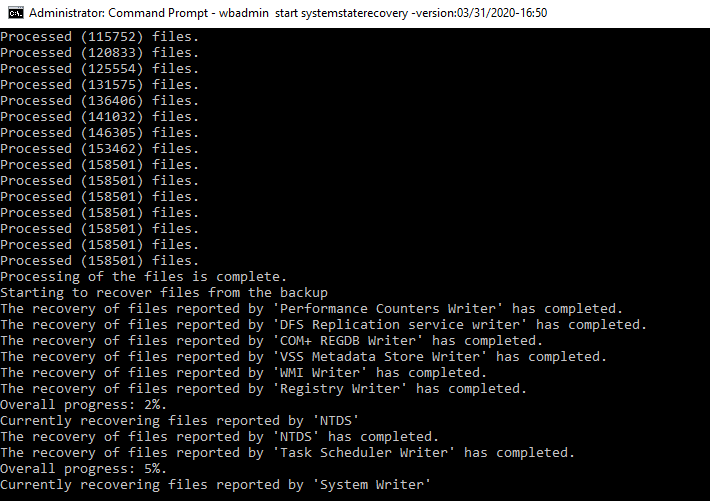
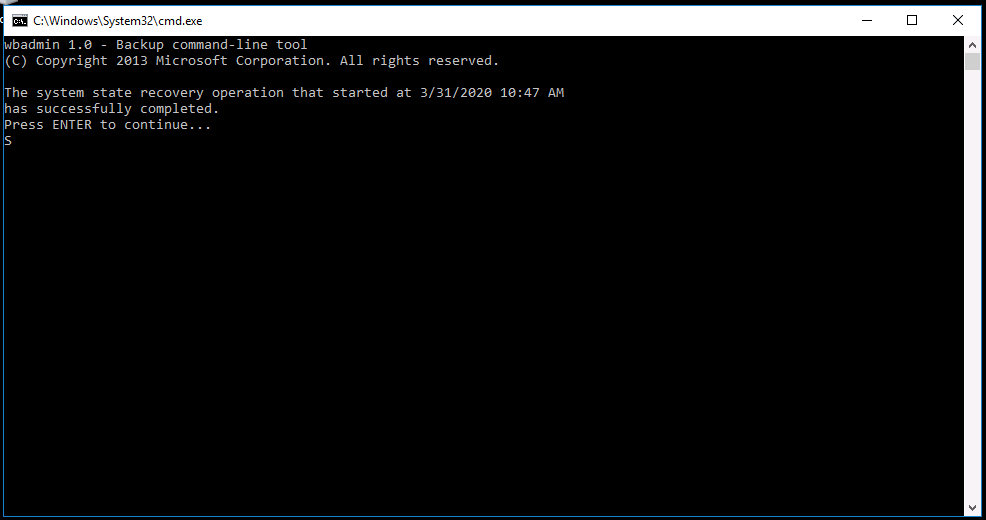
Finally, the backup will start and now it’s just a waiting game:
If you used MSConfig to start into DSRM mode, you will want to undo those changes before rebooting. Since my search doesn’t work, Im going to right-click the taskbar and select Task Bar.
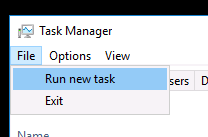
Next click File > Run new task
Type MSConfig and press OK. Go to Goot and turn off Safe boot:

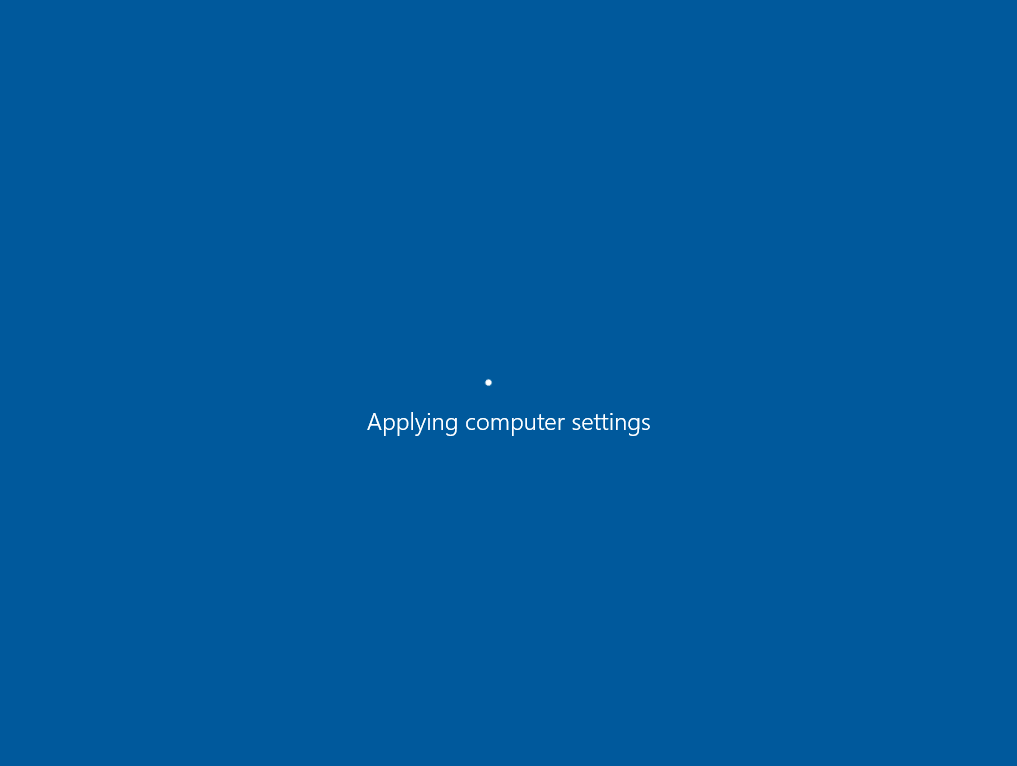
Now restart your server. The computer will take a while before booting up so you’ll need to be patient.
Once this is done, go ahead and log in. Once I open Active Directory I can see that the OUs and user accounts are now restored:
And that is how you perform an active directory backup and restore!

Server Academy Members Only
Sorry, this lesson is only available to Server Academy Full Access members. Become a Full-Access Member now and you’ll get instant access to all of our courses.



You mention backups being finished a couple of times, But I think you mean the restore is finished.
Hello i tried to replicate your steps on my vm and i did everything exactly the same as you.But when i tried to restore my Backup with Wbadmin after typing two times Yes for continuing it prompts me a “Windows Backup cant find the backup set directory on the media”
Any Idea whats the problem? I thought maybe its because the backup path is a network path but on the C:// ..
But when i did the WBadmin get versions it shows me the right backup files
thank you for helping
Interesting. Let me try it in a lab to give you a better answer Horst Bornschein-Grolms
Horst Bornschein-Grolms
Hi, I follow the steps on recovery and when machine running up I could not login. System did not want to accept CTRL+ALT+DELETE command, so I could not login again to check if I made it. Every time I pressed CTRL+ALT+DELETE the screen was flashing…
Hi Miroslav Ristic
Miroslav Ristic
If it is not responding to your commands you can try from the menu on VirtualBox selecting Input > Keyboard > Insert Ctrl-Alt-Del.
Ricardo
If there is a big server, for e.g. 600 TB which is almost full, but something happen and it brakes down. Lets say that we do have a backup, is there any shortcut to restore that amount of data again to the server or not? If not, that means that business have to suffer until everything is back. Or there is a shrotcut?
Hi Miroslav Ristic
Miroslav Ristic
Interesting question you ask, and might be the #1 concern of every sysadmin.
There might be different recovery options depending on the environment where that server sits. Restoring can take a significant amount of time. Having a high-bandwidth connections to move the data quickly can help. But with High Availability you can have the database replicated to another AD so if one crashes you can be up an running with a new one and once joined to the domain and promoted to AD the replication will take place.
In the worst case the business suffers the time you take to restore. The business takes into account these unexpected failures with Recovery Time Objective (RTO) and Recovery Point Objective (RPO). Disaster Recovery (DR) and High Availability (HA) can reduce the failure of the server breaking down.
Ricardo
I tried all the steps to Restore an active directory backup but once the computer restarts I don’t have internet connection, and I get a message saying “We can’t sign you in with these credentials because your domain isn’t available.”
Hi Ashi 3D,
Ashi 3D,
If you used the msconfig option to boot it might be going back to DSRM. In this mode networking gets disabled and you get that message when signing in to the domain without the local account.
Did the lab and followed the videos while I did the lab and on my end when I try to restore the back up is says there is no sysvol not sure what im doing wrong
Hi Kody Anderson
Kody Anderson
Let me ask a couple of questions since I have done it in the past and can’t replicate the issue. I even have done the previous section lab, the one where you add a second domain controller to perform the backup and then do the restore, following the videos.
When doing the backup are you just doing the system state backup? Do you use msconfig to enter DSRM mode? Do you use local lab in your PC or the online Labs? which one?
Ricardo
Safe boot and Online lab
Things to try can be: change permissions to the share folder to Everyone Full Control.
additionally you can try as well with the lab Lab: Adding a Second Domain Controller using SADC02 as your remote backup server using the Backup share folder under C:\ out of SADC01.
I tried the steps, did the sysvol command line and it prompts yes or no to start process, I say yes twice then I get the message that says “no SYSVOL component was found in the specified backup” did I miss a step?
I a sorry for the delay with your response Ashi 3D.
Ashi 3D.
I have seen that message. Let me do the lab and get back to you on why that is.
It seems from my tests on the lab that when doing the restore and using the –authsysvol flag you get that message, if you remove it the restore goes through.
I did a recovery backup of the data in ad of the IT LAB domain controller but after that process when I wanna go and see the data in AD users and computers it gives me that pop up of “Naming information cannot be located because the specified domain either does not exist or could not be contacted.
Hi Med Amine
Med Amine
Let me find a technical explanation to that message since every now and then I do the lab to experience the process and answer questions and sometimes I get the message and sometimes I don’t. Let me get back to you.
Ricardo
I did the lab twice and got the same error as you did. I am not sure but I will try once more using on the command prompt the restore option the –authsysvol option since the troubleshooting step that worked was editing the registry and
Click on start > Run >type regedit
Look for the SysvolReady entry under
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters\
SysvolReady was having a 0 value and I changed it to 1 then reboot once more.
This time it worked.
-Ricardo