Design Secure Access to AWS Resources
Secure access is one of the most important considerations when designing any AWS architecture. You should define how users, tools, and applications interact with AWS services and the data hosted there. This includes, for example, who can create or terminate AWS resources, when access is granted to your AWS resources, and any interactions involving AWS service calls.
AWS Root User
When you first create an AWS account, you begin with a single root user. This root user has unrestricted access to all resources and services in the AWS account. It is created using the email address and password you provided during the account setup process.
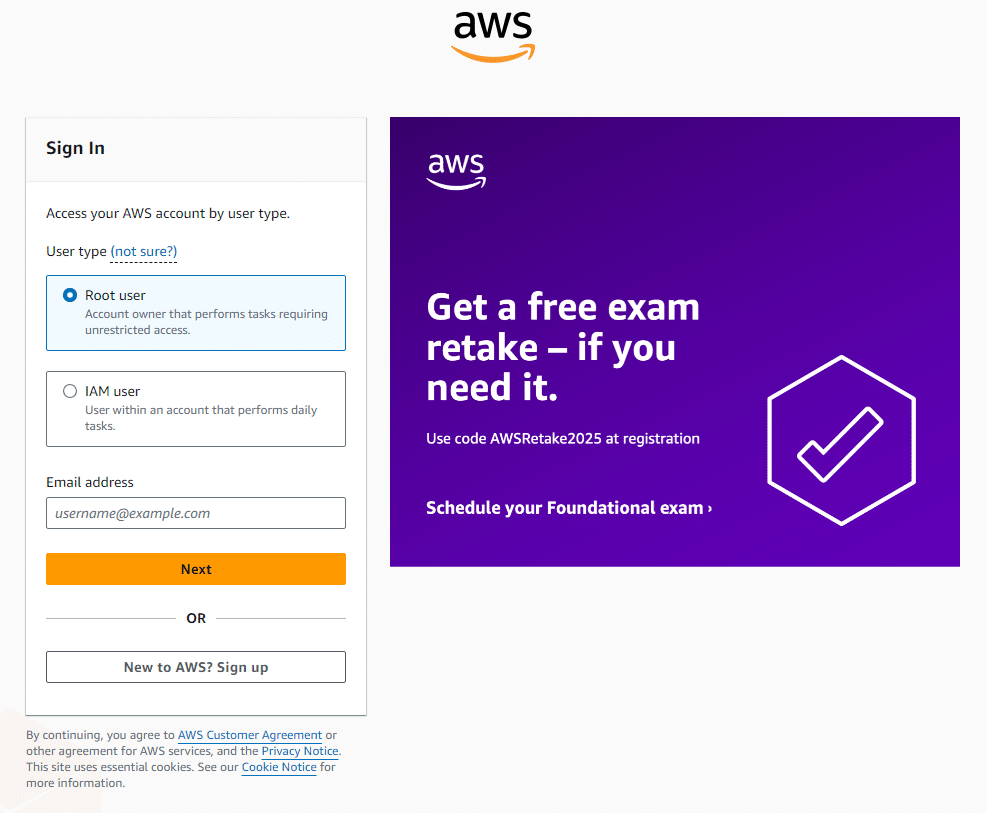 AWS Root User Login
AWS Root User Login
Why You Get the Root User:
- Initial Access: The root user is necessary for initial access to your AWS account. It allows you to set up the foundational aspects of your environment.
- Account Ownership: It serves as the primary means to verify account ownership and is required for certain account and billing activities that cannot be performed by other users.
Why You Should Not Continue to Use the Root AWS Account
While the root user is essential for initial setup, continuing to use it for daily operations poses significant security risks:
- Unrestricted Access:
- The root user has full permissions that cannot be restricted.
- Any actions performed using the root credentials affect the entire AWS account, including sensitive configurations and billing information.
- Increased Risk of Compromise:
- Using the root account increases the risk surface; if compromised, an attacker gains complete control over all resources.
- Root credentials are often targeted by malicious actors due to their elevated privileges.
- Lack of Accountability:
- Actions performed by the root user are harder to attribute to a s…
No comments yet. Add the first comment to start the discussion.